Nah, TCP is still just kicking the box over, but just kicking it over again, if the reciever doesn’t kick back a box saying they got it.
TCP is also deciding to ramp up the amount of boxes you kick over until the post worker gets crushed by boxes, at which point you decide to lower your box-kicking rate by half and try again.
Best explanation of congestion I’ve seen in a while
Well yes, internally that’s what it does, but from a user perspective it just looks like being handed the package, you never see any of the failed attempts (unless delivery fails completely because the company went out of business). It’s sorta more like having a butler who orders it for you and deals with any potential BS that might happen, and then just hands you the package when it finally arrives in one piece.
UDP seems more like a ball fired from canon to me. You may not be prepared for it and you won’t know what state it’s in when it gets here, but that packet is making it to the gate no matter what. Or, in the rare case it doesn’t, it means someone else is having a real bad time.
You forgot to mention that you might get it twice, or thrice, or more, and in different versions.
You’re right. I forgot that grapeshot is always something to worry about.
(novice) Why would you get UDP packets multiple times? UDP doesn’t check for acceptance I thought.
From StackOverflow:
Switches will send packets to all interfaces when using broadcasts or under extreme conditions (full MAC Address Table). This can lead to duplication if there is a loop between two or more switches and if the Spanning Tree Protocol is not used. So the answer is rarely.
https://stackoverflow.com/questions/9196791/duplicate-udp-packets-how-often-it-happens#9220574
That is extraordinarily rare and I’m not even sure if it’s possible anymore. That was potential attack vector in the 90’s where you have a port on network switch, and then you flood the cam table with thousands of bogus mac addresses until you fill it up, then the switch turns into a hub, and you can now sniff all traffic traversing the switch. These days I’m not sure what will happen if you do successfully fill up a switches cam table. Also cam table sizes are are much much larger now. ~128k entry’s vs maybe 1000 back in the day.
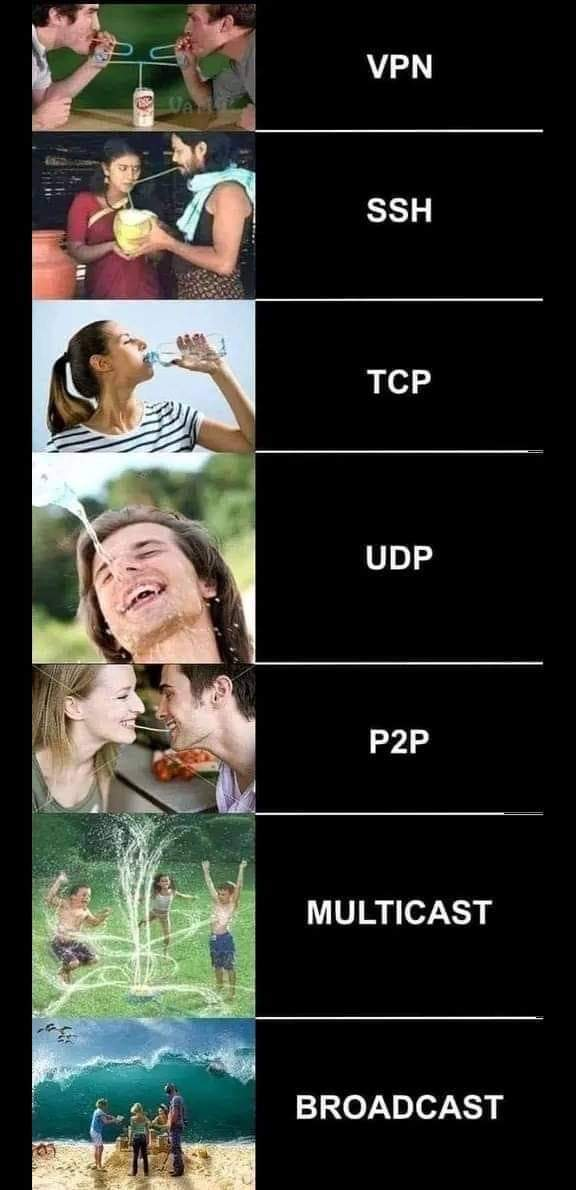
Jesus christ SSH
Can’t understand the VPN one shouldn’t the traffic pass through the VPN and then go to the user like the ssh one …
The person on the right of the VPN image is the destination server
Isn’t the can the vpn server and the guys are just vpn users?
that what I assumed
There’s nothing wrong with UDP. At least not that I know of.
I mean I’ve been trying to formally request that ISO change the C API for
send()toyeet()for sockets where connection reliability is not required at the network interface level.that’s fucking brilliant lol
That would be awesome! xD
Welp, time for a new language!
Well, thank you, now I’m creating that exact macro in every company repo where send/sendto is used.
ICMP
It’s a postcard saying “hey, thinking of you!” and there’s a picture of a wulrus on it.